Dynamsoft Developer Blog
Featured Content
View More >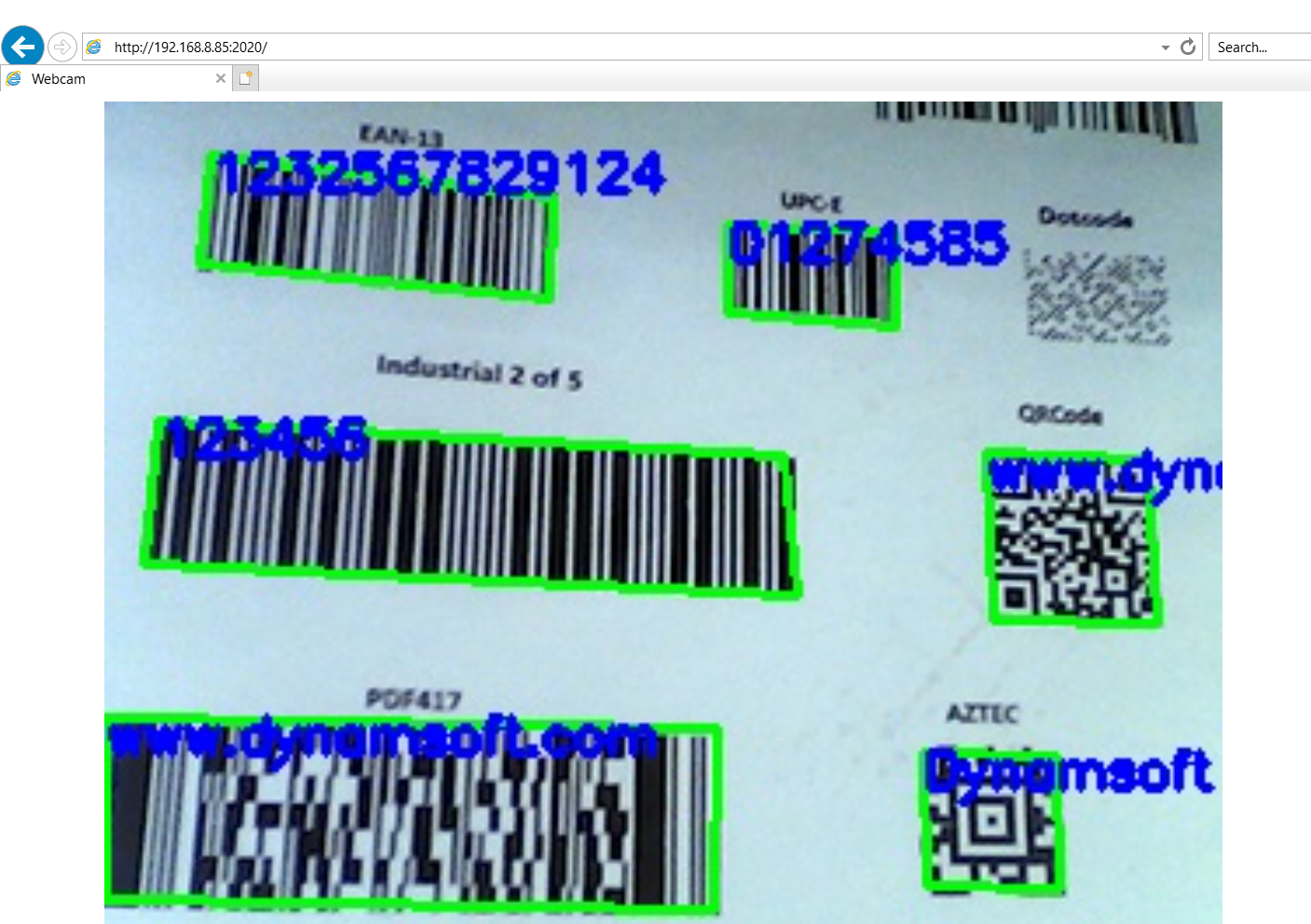
Node.js Barcode and QR Code Reader for Desktop and Web
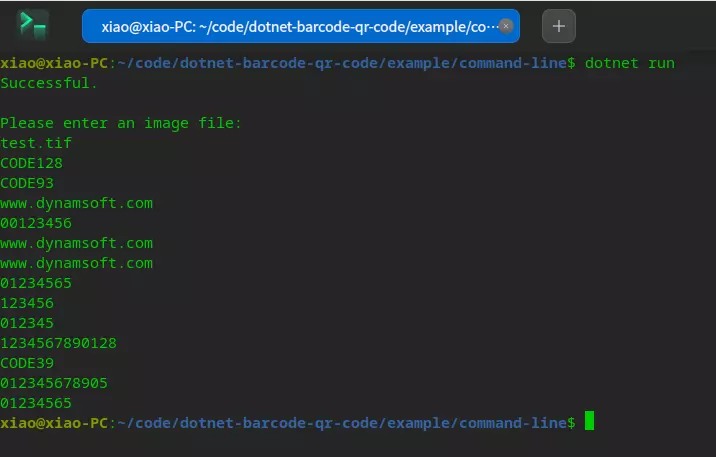
How to Build .NET 6 Barcode and QR Code SDK for Windows, Linux & macOS
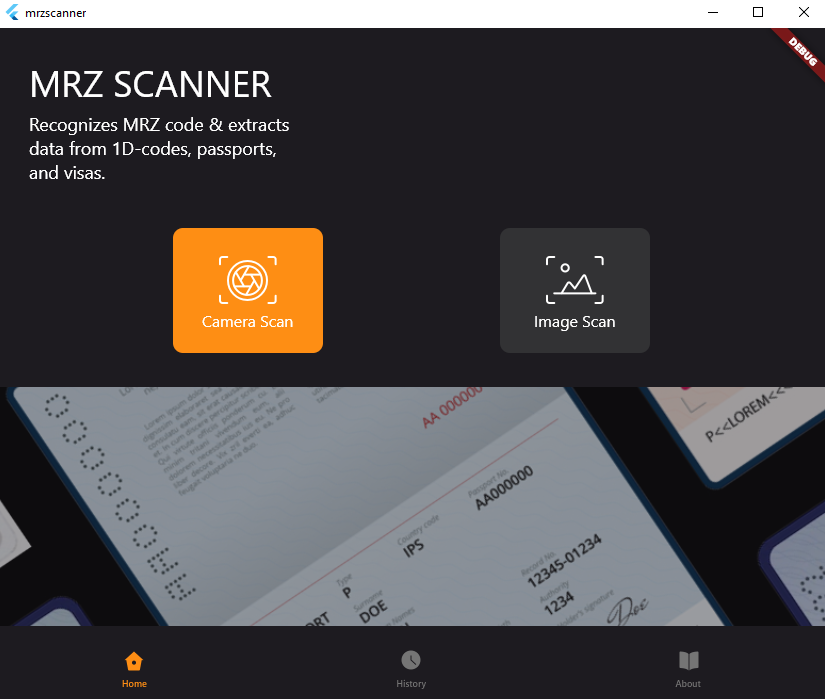
How to Create a Cross-platform MRZ Scanner App Using Flutter and Dynamsoft Label Recognizer
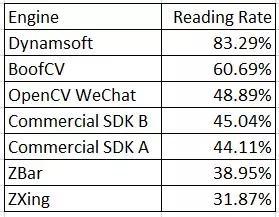
QR Code Reading Benchmark and Comparison
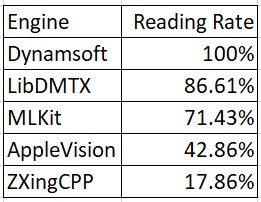
What are the Best Data Matrix Reading SDKs?
-
Mar 20, 2014 Miscellaneous
In this article, I will share the basic concept of Libwebsockets, as well as how to write a simple program with the APIs. What is Libwebsockets Libwebsockets is a lightweight pure C library; built to use minimal CPU and memory resources as well as providing fast throughput in both directions....
-
Mar 12, 2014 Miscellaneous
Previously, I talked about how to check PageRank in Java. In this article, I will combine PageRank with Excel files. To operate Excel files in Java, I used Apache POI - the Java API for Microsoft Documents. Apparently, you can download the API package, and follow the relevant tutorials to...
-
Mar 03, 2014 Miscellaneous
In this tutorial, let’s learn how to use OpenSSL to generate X.509 certificate request. Certificate signing request is a message sent from an applicant to a certificate authority, which usually includes: Country Name (2 letter code) [US] State or Province Name (full name) [BC] Locality Name (e.g., city) [Vancouver] Organization...
-
Feb 26, 2014 Miscellaneous
It is known that RSA is a cryptosystem which is used for the security of data transmission. This tutorial introduces how to use RSA to generate a pair of public and private keys on Windows. Download and install OpenSSL https://www.openssl.org/community/binaries.html. Find libeay32.lib, ssleay32.lib and libeay32.dll. The following sample code will...
-
Feb 11, 2014 Miscellaneous
Backlink is one of the most important factors for search engine ranking. Thus, the analysis of backlinks is significant for website owners. It is known that Google Webmaster tools can record search traffic allowing users to check the links to their sites. We can download the relevant data as figure...
-
Feb 07, 2014 Miscellaneous
Strong name signatures consist of the identities of an assembly. They are strengthened by both public keys and digital signatures (as generated from the assembly). The identities include the plain text name, version number and regional information of the assembly (if provided). An assembly with a strong name can only...
-
Dec 19, 2013 Miscellaneous
Yesterday, my colleague told me that there was a weird issue that existed in our WPF sample code for Dynamic .NET TWAIN. What we wanted to implement was to create two projects, and start one application from another. The problem was, when we started the invoked application independently, it worked...
-
Sep 12, 2013 Document Scanning
In today’s “big data era”, more and more organizations are using an enterprise content management (ECM) or record management system (RMS) to help maintain and manage the documents. Digitizing documents and storing them in a central database has become an important part of many organization’s document management workflow. For this...
-
Jul 28, 2013 Barcode
Barcode scanning, especially QR code scans, are now widely used in various applications. This includes advertisements, newspapers, social networks, signage, and so on. The growth of QR codes is in large part due to the smartphone market’s booming growth. As a result, scanning technology tends to be more and more useful...
-
Jul 01, 2013 Version Control
Sometimes you may want to switch to another user to log into your Team Foundation Server (TFS) service. However, you would find that Windows remembers your credentials and log you in automatically. So how to make TFS forget the old credentials so that you can get the chance to enter...